Part 1 Advanced The Market Maker’s Exchange Checklist (Liquidity, Latency, and Risk Controls) Market makers and HFT desks: evaluate exchanges on execution quality, liquidity, latency, fees, margin, and security — with a WhiteBIT walkthrough. Open guide
Part 1 Advanced The Market Maker’s Exchange Checklist (Liquidity, Latency, and Risk Controls) Market makers and HFT desks: evaluate exchanges on execution quality, liquidity, latency, fees, margin, and security — with a WhiteBIT walkthrough. Open guide Bitcoin Cash reportedly suffered a 51% attack, transactions reversed

Cover art/illustration via CryptoSlate. Image includes combined content which may include the use of AI tools.
Bitcoin Cash reportedly suffered a 51% attack following its May 15 scheduled hardfork upgrade.
Following Bitcoin Cash’s hardfork upgrade, an attacker exploited a vulnerability in the update that added invalid transactions to the pool of unprocessed transactions (the Mempool). One source claims these were “poison” transactions that made it so miners were unable to participate in mining.
The exploit crippled the network for an hour and a half. The majority of miners were unable to participate in consensus, while those remaining were only able to mine mostly empty blocks.
Another source suggests that BTC.TOP opted to mine empty blocks to continue reaping mining rewards.
“Since most other miners were offline at the time due to the exploit, BTC.TOP controlled over half of the Bitcoin Cash network hash power, allowing them to determine which blocks were accepted by the network,” said Guy Swann, host of the Cryptoconomy Podcast.
During the chaos, BTC.TOP—potentially in collusion with another dominant mining pool, BTC.com—conducted a “non consensus re-org.” There are claims that the move constitutes a 51% attack on the Bitcoin Cash blockchain.
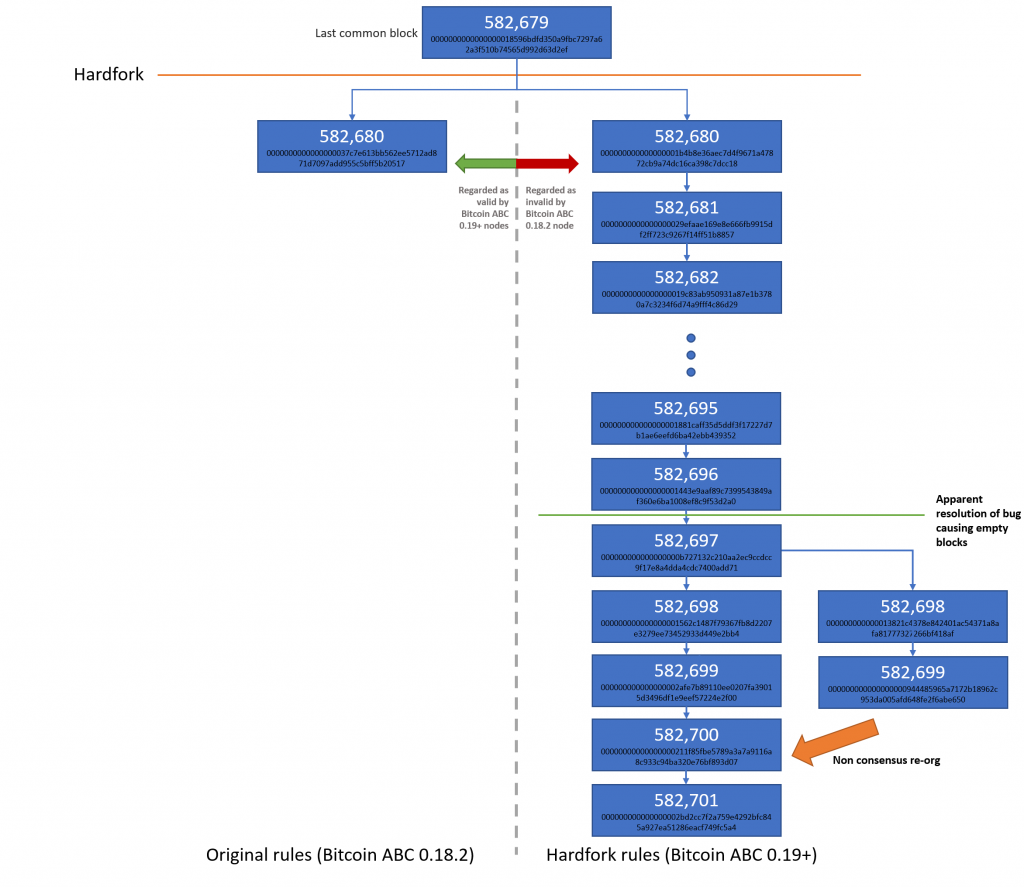
The actions were said to have been motivated by the reclamation of previously unspendable BCH. A prior update on Bitcoin Cash made it so coins sent to particular addresses were unspendable. However, the May 16 hardfork changed that rule:
“This upgrade will make an exemption for these coins and return them to the previous situation, where they are spendable… any miner can take the coins,” stated the Bitcoin Cash GitHub.
An unknown miner then attempted to claim these previously unspendable coins, said Aaron van Wirdum, technical editor at Bitcoin Magazine.
“When an unknown miner claimed these coins, the BTC.com and BTC.TOP pools coordinated [a] 51%-attack to return coins to original owners.”
If verified, this could prove a major blow to Bitcoin Cash. “This basically kills any perception that Bitcoin Cash is ‘decentralized, censorship-resistant money,” said Swann.
Read on for the details on how 51% attacks are executed.