 Part 1 Beginner Why long-term crypto holders borrow against assets instead of selling A strategic guide to liquidity management, capital preservation, and the real tradeoff between selling and borrowing crypto Open guide
Part 1 Beginner Why long-term crypto holders borrow against assets instead of selling A strategic guide to liquidity management, capital preservation, and the real tradeoff between selling and borrowing crypto Open guide Adobe Flash Being Used For Cryptojacking
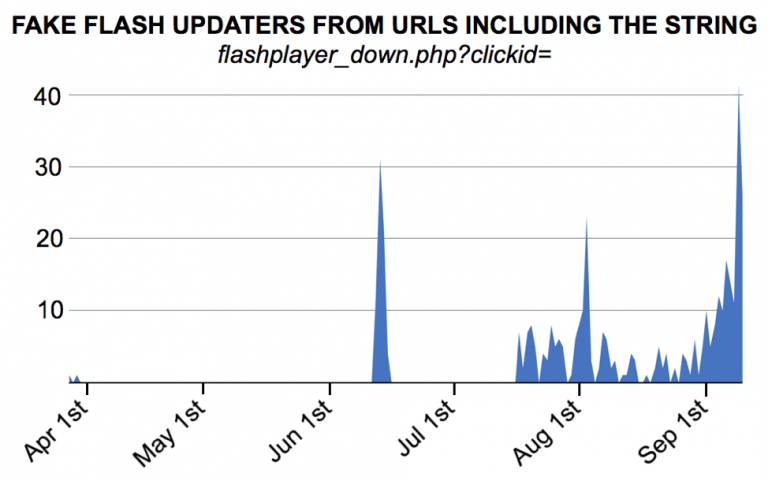
Cybersecurity software company Palo Alto Networks reports that miners looking to use your computer to expand their hashing power are getting sneakier. New fake Adobe updates are circulating that will actually update the plugin on your computer, but also install illicit mining malware.
Hiding Behind Legitimate Sofware
These fakes are especially insidious because they do install the correct program along with the malware, fooling the user into believing that the update is legitimate.
As in other instances of illicit mining, the hackers are going after Monero, who’s mandatory privacy protocol makes it extremely hard to trace. The fake installer updates Adobe Flash on the victim’s computer while installing XMRig in the background. The hidden program then uses the host computer’s processing power and graphics card to mine Monero without them knowing.
Over one hundred of these fake update programs have been found by Palo Alto since March, according to TechCrunch. As the XMRig software page lists an idle operating system is ideal for maximum efficiency, its likely that this malware activates when a host computer isn’t being used.
Flash has long been a favorite method for installing malware on the systems of unsuspecting users, which, along with updates to the web like HTML5 meaning Flash use is on the decline, probably contributed to Adobe’s decision to kill it in 2020.
The Problem of Illicit Mining Malware Continues
Illicit mining has grown exponentially this year, as stated in a report released by the Cyber Threat Alliance (CTA) last month. Hackers are using fake installers like the one discovered by Palo Alto Networks, but also exploiting vulnerabilities like Eternal Blue which allow them easy access to older systems. Once in, they install similar hidden malware that hijacks a computer into their mining network.
CTA Chief Analytical Officer Neil Jenkins stated that cryptojacking is the “canary in the coal mine” of attacks because bad actors could exploit the same vulnerabilities used in cryptojacking for even more nefarious purposes. The executive summary report includes:
“Illicit cryptocurrency mining is the figurative canary in the coal mine, warning you of much larger problems ahead. CTA members recount case after case of being called into an incident response for a mining infection and finding signs of multiple threat actors in the network.”
Users may be wise to stick to newer protocols that don’t require the use of Flash, scan their systems regularly for malware with a reliable program, and be wary of any update notifications they might not recognize. Palo Alto Networks provides an appendix of fake updater examples and tips on how to spot them in their blog post.
Unit 42 investigates a recent Fake Flash update pushing cryptocurrency mining software. Get the full report https://t.co/qGt1Z1NNHw pic.twitter.com/ZejZE3sDpI
— Unit 42 (@Unit42_Intel) October 11, 2018










































