Part 1 Advanced The Market Maker’s Exchange Checklist (Liquidity, Latency, and Risk Controls) Market makers and HFT desks: evaluate exchanges on execution quality, liquidity, latency, fees, margin, and security — with a WhiteBIT walkthrough. Open guide
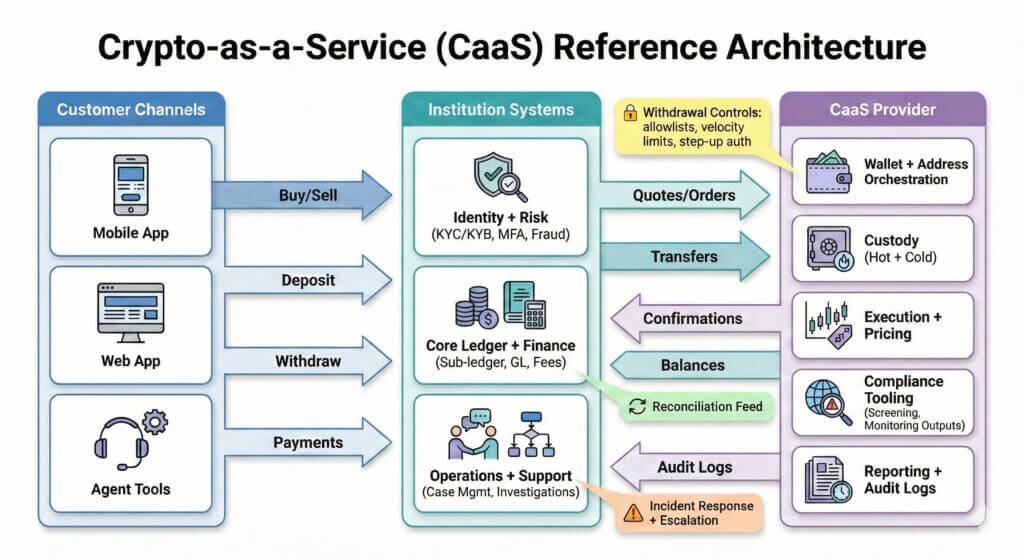
Part 1 Advanced The Market Maker’s Exchange Checklist (Liquidity, Latency, and Risk Controls) Market makers and HFT desks: evaluate exchanges on execution quality, liquidity, latency, fees, margin, and security — with a WhiteBIT walkthrough. Open guide Crypto-as-a-Service (CaaS) is the “build crypto products without building a crypto exchange” approach. Your institution keeps the customer relationship, product governance, and brand experience; a specialist provider supplies wallet infrastructure, execution rails, custody options, and operational tooling to run crypto safely at scale.
This matters because most regulated institutions do not fail on “can we build it.” They fail on operational risk: custody controls, fraud, reporting, and the day-two responsibilities that come after launch.
In this guide, you will learn:
- Why banks, telcos, and fintechs are revisiting crypto products now, without relying on hype
- What CaaS includes (and what it does not) for procurement, risk, and compliance teams
- A reference architecture for integrating a CaaS stack into identity, core ledger, and support tooling
- A phased rollout plan for a “minimum viable crypto product,” including the guardrails that prevent regrets
- How to evaluate security, custody, compliance workflows, payments rails, economics, and vendors
Who this guide is for: fintechs, banks, neobanks, telcos, payment providers early in crypto adoption, plus brokerages and smaller exchanges adding rails.
Disclaimer: Informational only, not financial, legal, or compliance advice. Regulations vary by jurisdiction; involve your legal and compliance teams early.